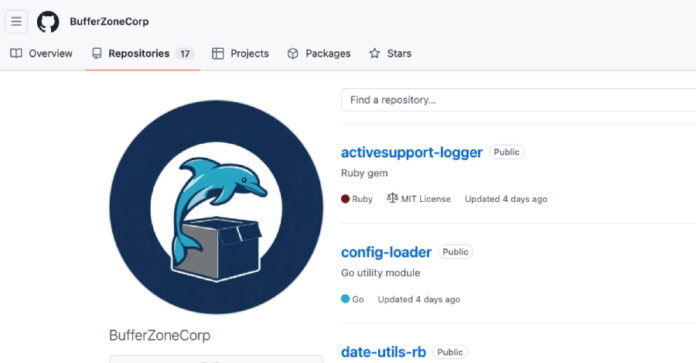
A software supply chain attack campaign has been identified using sleeper packages to distribute malicious payloads capable of stealing credentials, tampering with GitHub Actions, and establishing SSH persistence. The activity has been linked to the GitHub account BufferZoneCorp, which published repositories containing malicious Ruby gems and Go modules.